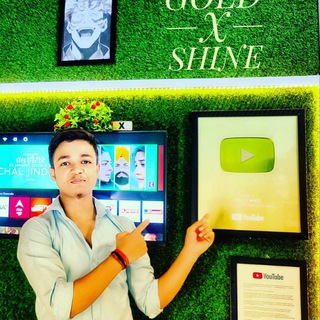
*Connect our social apps for letest update 📍*money hi money
*Teligram channel 👇*
https://t.me/pythanprince
*YouTube channel 👇*
http://www.youtube.com/@CodeWithPrince21
*Instagram I'd 👇*
instagram.com/prince_sharma_872?igsh=MW55MWppdWNsZDhjMg==
My Personal Mentorship GRP 🖇
Mo. 9457648556
Only for msg......
*Teligram channel 👇*
https://t.me/pythanprince
*YouTube channel 👇*
http://www.youtube.com/@CodeWithPrince21
*Instagram I'd 👇*
instagram.com/prince_sharma_872?igsh=MW55MWppdWNsZDhjMg==
My Personal Mentorship GRP 🖇
Mo. 9457648556
Only for msg......
Telegram
Pythanprince
👉past can never changes but we can change future workhard today👈
🐉 Kali Linux: Complete Guide to Ethical Hacking Tools and Their Uses
Jan 28, 2026
—
by
Prince Sharma
in Uncategorized
(Kali Linux official identity is the dragon logo — symbol of power, security, and control)
🔍What Is Kali Linux?
Kali Linux is a Debian-based Linux distribution designed for ethical hacking, penetration testing, cybersecurity research, and digital forensics. It is developed and maintained by Offensive Security and is used by security professionals worldwide.
Kali Linux comes with 600+ preinstalled tools for security testing and learning.
🧠 Why Kali Linux Is So Powerful
Built specifically for cybersecurity
Trusted by professionals and organizations
Free & open-source
Regularly updated tools
Supports beginners to experts
⚠️ Important: Kali Linux must be used only for legal and educational purposes.
🧰 Major Kali Linux Tools and Their Uses
🔹 1. Nmap (Network Mapper)
🛠 Use: Network scanning & discovery
Finds open ports
Detects devices on a network
Checks security vulnerabilities
🔹 2. Metasploit Framework
🛠 Use: Penetration testing
Exploits known vulnerabilities
Tests system security
Used by professional ethical hackers
🔹 3. Wireshark
🛠 Use: Network traffic analysis
Captures live network data
Analyzes packets
Detects suspicious activity
🔹 4. Aircrack-ng
🛠 Use: Wireless security testing
Tests Wi-Fi security strength
Detects weak encryption
Used to audit wireless networks
🔹 5. Burp Suite
🛠 Use: Web application security
Finds website vulnerabilities
Tests login forms & APIs
Used by web security testers
🔹 6. Hydra
🛠 Use: Password testing
Tests password strength
Supports multiple protocols
Used for security audits
🔹 7. John the Ripper
🛠 Use: Password cracking (ethical)
Tests password strength
Helps improve authentication security
🖥 Who Should Use Kali Linux?
✔️ Cybersecurity students
✔️ Ethical hackers
✔️ Penetration testers
✔️ Network administrators
✔️ Digital forensics learners
🚀 Benefits of Learning Kali Linux
High-demand cybersecurity skills
Career opportunities
Deep understanding of system security
Strong foundation in ethical hacking
🔐 Legal & Ethical Reminder
Kali Linux tools are powerful.
Using them without permission is illegal.
Use Kali Linux only on systems you own or have written permission to test.
🧠 Final Thoughts
Kali Linux is not just an operating system — it is a complete cybersecurity ecosystem. When used responsibly, it helps secure systems, protect data, and build strong digital defenses.
🔍 SEO DETAILS
Focus Keyword:
Kali Linux tools and uses
Meta Description:
Learn everything about Kali Linux, its powerful ethical hacking tools, and their real-world uses. A complete beginner-friendly guide to Kali Linux.
❤️ Support the Blog
If you found this post helpful:
👍 Like the post
💬 Comment your thoughts
🔔 Subscribe for more tech & cybersecurity content
I Will tell everything about development and many other stay HERE and Support me ( We will construct many project here )
YOUTUBE—-
www.youtube.com/@CodeWithPrince21
TELEGRAM—-
t.me/pythanprince
Jan 28, 2026
—
by
Prince Sharma
in Uncategorized
(Kali Linux official identity is the dragon logo — symbol of power, security, and control)
🔍What Is Kali Linux?
Kali Linux is a Debian-based Linux distribution designed for ethical hacking, penetration testing, cybersecurity research, and digital forensics. It is developed and maintained by Offensive Security and is used by security professionals worldwide.
Kali Linux comes with 600+ preinstalled tools for security testing and learning.
🧠 Why Kali Linux Is So Powerful
Built specifically for cybersecurity
Trusted by professionals and organizations
Free & open-source
Regularly updated tools
Supports beginners to experts
⚠️ Important: Kali Linux must be used only for legal and educational purposes.
🧰 Major Kali Linux Tools and Their Uses
🔹 1. Nmap (Network Mapper)
🛠 Use: Network scanning & discovery
Finds open ports
Detects devices on a network
Checks security vulnerabilities
🔹 2. Metasploit Framework
🛠 Use: Penetration testing
Exploits known vulnerabilities
Tests system security
Used by professional ethical hackers
🔹 3. Wireshark
🛠 Use: Network traffic analysis
Captures live network data
Analyzes packets
Detects suspicious activity
🔹 4. Aircrack-ng
🛠 Use: Wireless security testing
Tests Wi-Fi security strength
Detects weak encryption
Used to audit wireless networks
🔹 5. Burp Suite
🛠 Use: Web application security
Finds website vulnerabilities
Tests login forms & APIs
Used by web security testers
🔹 6. Hydra
🛠 Use: Password testing
Tests password strength
Supports multiple protocols
Used for security audits
🔹 7. John the Ripper
🛠 Use: Password cracking (ethical)
Tests password strength
Helps improve authentication security
🖥 Who Should Use Kali Linux?
✔️ Cybersecurity students
✔️ Ethical hackers
✔️ Penetration testers
✔️ Network administrators
✔️ Digital forensics learners
🚀 Benefits of Learning Kali Linux
High-demand cybersecurity skills
Career opportunities
Deep understanding of system security
Strong foundation in ethical hacking
🔐 Legal & Ethical Reminder
Kali Linux tools are powerful.
Using them without permission is illegal.
Use Kali Linux only on systems you own or have written permission to test.
🧠 Final Thoughts
Kali Linux is not just an operating system — it is a complete cybersecurity ecosystem. When used responsibly, it helps secure systems, protect data, and build strong digital defenses.
🔍 SEO DETAILS
Focus Keyword:
Kali Linux tools and uses
Meta Description:
Learn everything about Kali Linux, its powerful ethical hacking tools, and their real-world uses. A complete beginner-friendly guide to Kali Linux.
❤️ Support the Blog
If you found this post helpful:
👍 Like the post
💬 Comment your thoughts
🔔 Subscribe for more tech & cybersecurity content
I Will tell everything about development and many other stay HERE and Support me ( We will construct many project here )
YOUTUBE—-
www.youtube.com/@CodeWithPrince21
TELEGRAM—-
t.me/pythanprince
Telegram
Pythanprince
👉past can never changes but we can change future workhard today👈